Copyright Management Information (CMI) is the identifying data that accompanies a creative work, such as title, author, copyright owner, and usage terms. This information is often embedded in metadata or displayed with the work. In the modern digital age, this information plays a crucial role in managing rights and preventing copyright infringement. U.S. copyright law, particularly the Digital Millennium Copyright Act (DMCA), provides legal protections for the integrity of CMI. Business owners and creators need to understand what CMI is, why it matters, and how U.S. law treats the removal or alteration of CMI. This article discusses the purpose of CMI, the legal claims related to it, enforcement and litigation trends, best practices for compliance, and a brief look at how foreign jurisdictions handle Copyright Management Information. The goal is a professional yet accessible overview for non-specialists, with relevant statutes and case law cited along the way.
Copyright Management Information is defined by law as certain information conveyed in connection with copies or performances of a work, including in digital form, that identifies the work or its rights holders. In practice, CMI can be found in visible notices or hidden metadata attached to creative content. For example, CMI may include:
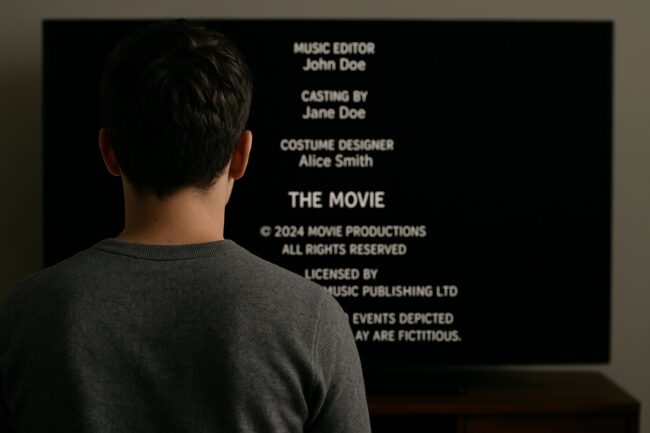
This information is typically provided alongside the work to inform the public about who created it, who owns it, and how it can be used. A common example of Copyright Management Information is the © notice on a book or the metadata in a digital photo file that lists the photographer’s name and copyright details. In an audiovisual work, CMI may be embedded information in the file itself and there may be on-screen credits. It’s important to note that CMI specifically does not include any personally identifying information about a user of the work. In other words, the law is concerned with information identifying the work and its owners, not the identities of people who might access or use the work.
Copyright Management Information can appear in both analog and digital form, but it has become especially crucial in digital media. Metadata tags in MP3 files, EXIF data in images, watermarks on videos, QR codes or hyperlinks that link to license info, and other such information qualifies as CMI if they convey identifying information about the copyrighted work.

The primary purpose of CMI is to preserve the link between a creative work and its rightful owner or creator, thereby facilitating legitimate use and licensing of the work. By ensuring that a work’s origin and terms of use are clear, CMI helps users know how they can lawfully use the content and whom to contact for permissions. From a policy perspective, Congress enacted protections for CMI to uphold the integrity of copyright management and reduce infringement. If accurate CMI stays intact with the work, it becomes easier to manage rights, e.g., to locate the owner for licensing, and harder for others to infringe under the guise of ignorance.
In legislative history, officials emphasized two key goals of protecting CMI. First, requiring the preservation of CMI makes it more reliable and aids in the “administrability of copyright law”, meaning it’s easier to enforce rights when works are properly attributed. Second, it helps prevent copyright infringement that could occur when CMI is removed. The reasoning is simple: if a work is stripped of credit or copyright notice, people might assume it’s free to use or even try to pass it off as their own. For instance, if someone finds a photo online with no attribution or notice, such person might reuse it without realizing it’s protected. By discouraging the removal of CMI or penalizing it after the fact, the law aims to “induce, enable, [or] facilitate” the proper use of works and not to enable or conceal infringement. In effect, CMI protection serves as a form of damage control against potential copyright abuse. It safeguards the informational infrastructure that underpins licensing and enforcement.
In summary, CMI exists to inform and protect: it informs the public about ownership and allowed uses, and it protects creators by reducing anonymity of works. When used consistently (e.g. always including a copyright notice or metadata), CMI can help copyright owners maintain their brands and rights, and it can serve as evidence in court of willful infringement if someone deliberately removes or alters it.
In the United States, the Digital Millennium Copyright Act (DMCA) of 1998 introduced specific provisions to protect CMI as part of a broader effort to combat digital copyright abuse. Section 1202 of Title 17, U.S. Code (“Integrity of copyright management information”) is the key statute. It implements obligations from international treaties (the WIPO Copyright Treaty’s Article 12) by making it unlawful to falsify or tamper with CMI. This section is part of Chapter 12 of the Copyright Act, which deals with technological protection measures and rights-management information: hence the chapter’s name “Copyright Protection and Management Systems”.
Definition of CMI
As described earlier, §1202(c) defines “copyright management information” to include various identifying details about a work (title, author, owner, terms of use, etc.), including in digital form. The statute explicitly excludes any personally identifying information about users from the definition, focusing only on information about the work or its creators/owners. Notably, the definition even covers identifying numbers and symbols that refer to CMI, as well as links to such information. For example, a barcode or embedded link that, when scanned, provides the copyright details qualify as CMI.
False CMI (Section 1202(a))
The law prohibits providing false copyright management information or distributing false CMI, when done knowingly and with an intent to facilitate infringement. Specifically, no person shall knowingly and with the intent to induce, enable, facilitate, or conceal infringement:
In plain terms, this targets situations where someone might attach incorrect or fake ownership information to a work. For example, if a person removed an original watermark and added their own name (false CMI) to a photograph in order to claim it as theirs, that would violate §1202(a) by knowingly providing false CMI with intent to enable or conceal infringement. False CMI cases are less common, but the provision exists to punish attempts to mask infringement by falsifying the attribution or rights info of a work.
Removal or Alteration of CMI (Section 1202(b))
This is the heart of CMI protection and a scenario that frequently arises in practice. Section 1202(b) makes it unlawful to intentionally remove or alter CMI without authority, or to distribute works or CMI knowing that CMI was removed or altered without authority, if done knowing (or having reasonable grounds to know) that such actions will “induce, enable, facilitate, or conceal” copyright infringement. Breaking that down:
To illustrate, imagine a website operator knowingly strips metadata (which contains the photographer’s name and copyright notice) from images before posting them. If at the time of removal the operator has reasonable grounds to know that this act will make it easier for users to download and reuse those images without permission (thus infringing), the operator could be liable under §1202(b). The knowledge can be actual or inferred, and it covers acts that “enable or conceal” infringement. For example, removing CMI can conceal the infringement by making it harder to trace the work back to the owner, or enable infringement by removing warnings or watermarks that would otherwise deter copying.
It’s worth noting that the infringement in question need not be by a third party. Courts have confirmed that removing CMI to cover up one’s own infringing use counts. In one case, a media company published a photographer’s image without permission and replaced the photographer’s credit with a different name, thereby concealing its unauthorized use. The court held this satisfied the statute’s scienter requirement because the removal concealed the company’s infringement. No separate “future” infringer was required.
In short, if you intentionally remove or alter CMI on a copyrighted work without consent, and you know or should know that doing so could lead to copyright infringement, you are violating §1202(b).
While the law is strict about not removing or altering CMI, it provides some exceptions and safe harbors for certain activities and industries. These ensure that legitimate governmental or technical reasons for removing CMI are not wrongly penalized.
Law Enforcement and Government Activities
Section 1202 includes an exception for lawful investigative, protective, or intelligence activities by government officials or those contracted by the government. This means that if a federal or state law enforcement officer, or an agent engaged in national security or similar intelligence operations, removes CMI as part of an authorized investigation or security test, §1202 does not apply. For instance, a government cybersecurity team analyzing a breach might copy files and strip certain info for analysis. The statute explicitly says it “does not prohibit any lawfully authorized investigative, protective, information security, or intelligence activity” by government officers or those acting under government contract. The term “information security” include activities performed to identify or address vulnerabilities in government computers, systems, and/or networks. In short, bona fide government operations (law enforcement, national defense, cybersecurity) can involve removal of CMI without triggering liability.
Broadcast and Transmission Safe Harbors: The statute also creates specific safe harbors for broadcasters (like radio and television stations) and cable providers when transmitting works, acknowledging that inserting or retaining CMI in certain broadcasts may be technologically difficult or incompatible with broadcast standards. These are technical exceptions mostly relevant to broadcasting businesses:
Additionally, the law carves out certain content from the definition of CMI for broadcasters. Notably, §1202(c) excludes performer information from being treated as CMI in the context of live broadcasts by radio and television stations. For example, in the case of a publicly performed work in a live radio concert, the name of a performer isn’t considered protected CMI under this section to avoid burdening live broadcasters with adding credits for every performance in real-time. So, while a performer’s name is generally CMI for recorded works, the law doesn’t penalize radio and TV stations for not displaying or transmitting performer info during live public performances.
The key takeaway is that unless you fall into a narrow exception, like law enforcement or constrained broadcast scenarios, you should not remove or alter CMI without permission. The vast majority of commercial activities (e.g., posting images online, republishing articles, editing videos) are expected to preserve any CMI that comes with the content. If you have authorization from the copyright owner to remove CMI (e.g., a license allowing you to use a photo without credit), that constitutes “authority of the copyright owner” under the statutory language and is not a violation. But absent such permission or a specific legal exemption, removing metadata, watermarks, or notices is risky under the DMCA.
Under §1203 of the Copyright Act, anyone injured by a violation of 17 U.S.C. §1201 or §1202 can bring a civil lawsuit in federal court. This means if someone removed your work’s CMI or added false CMI and it harmed you (e.g., by making it easier to infringe your work or cause loss of licensing revenue), you can sue that person in an appropriate U.S. district court. Claims against such violations are often brought alongside direct copyright infringement claims, but they are distinct causes of action. You can sue for CMI removal even if the underlying use might have been licensed or at least even if no separate infringement claim is proven, as long as the statutory criteria are met.
When a court finds a violation, it has broad powers to redress the harm and deter further abuses. Key civil remedies available include:
Thus, while attorneys’ fees and costs can serve as powerful tools to make litigation viable for smaller rightsholders and as deterrents against willful violators, their availability is ultimately discretionary. Parties bringing or defending CMI-related claims should be mindful that the court will weigh the overall reasonableness and policy implications of awarding fees, rather than applying a bright-line rule.
In addition to civil remedies, there are criminal provisions for willful CMI violations. Under 17 U.S.C. §1204, if someone willfully violates §1201 or §1202 for purposes of commercial advantage or private financial gain, they can face criminal fines and even imprisonment. For a first offense, the penalty can be up to $500,000 in fines or 5 years in prison (or both); for repeat offenses, up to $1,000,000 or 10 years in prison. Nonprofit institutions are exempt from criminal liability. While criminal prosecutions under §1202 are rare, the presence of these penalties underscores the seriousness of CMI violations. For a business owner, this means that systematically removing CMI for profit (e.g., a scheme to scrape copyrighted images, strip metadata, and resell them) could potentially lead to federal criminal charges, not just civil lawsuits.
In real-world litigation, CMI claims have presented some challenges and evolving interpretations. Courts have grappled with exactly what a plaintiff must prove to succeed under §1202(b). Two major issues in enforcement are: (1) proving the knowledge/intent element (scienter), and (2) the scope of works covered (the “identicality” issue).
Knowledge (“Double Scienter”) Requirement
As noted, §1202(b) requires the defendant knew or had reasonable grounds to know that their removal or alteration of CMI would likely facilitate infringement. The argument that it should be enough to show the removal could make infringement easier in a general sense is not enough. Recent appellate decisions have set a higher bar. The Second Circuit, Ninth Circuit, and Eleventh Circuit all require an affirmative showing that the defendant was aware that removal of CMI would likely lead to specific infringing acts. In Stevens v. CoreLogic, Inc., 893 F.3d 648 (9th Cir. 2018), for example, a group of photographers claimed a software company stripped metadata (CMI) from their photos. The Ninth Circuit rejected the claim because the photographers failed to produce evidence showing that the defendant knew its software carried even a substantial risk of concealing infringement, let alone a likelihood of actual infringement resulting. The court held that §1202(b) requires a showing that the defendant knew the prohibited act would "‘induce, enable, facilitate, or conceal’ infringement,” and mere conjecture was not enough.
The defendant’s state of mind matters greatly. Innocent or purely technical removal is not the target, knowing removal that is oriented toward making infringement easier is. For plaintiffs (e.g. content creators enforcing their rights), this means gathering evidence not just that CMI was removed, but that the remover understood the significance. Evidence might include internal emails about scrubbing metadata to avoid “takedown notices,” patterns of removed CMI followed by widespread uncredited use, or admission that the remover knew permission was needed. For defendants, the “double scienter” standard is a shield against tenuous claims. If they truly didn’t think about infringement resulting, they may avoid liability, though pushing “ignorance” too far can be risky if a reasonable person would have seen the risk.
“Identicality” of the Work
A newer debate in CMI litigation is whether the statute only applies when the work distributed without CMI is exactly the same as the original work apart from the missing CMI. Some courts have imposed an “identicality requirement”, essentially requiring that the defendant distributed an identical copy of the copyrighted work with CMI removed, as opposed to a modified or partial version. Under this view, if the work was altered significantly or only a portion of the work was used, a §1202(b) claim might not lie because the statute speaks in terms of copies of works and removal of CMI from the work. For example, one court held that taking a photographer’s image and reproducing it in full without the metadata met identicality (the only change was removing CMI), whereas using snippets or creating a derivative might not.
Not all courts agree on this. Some have explicitly rejected the identicality requirement, arguing it isn’t found in the statutory text and would undermine protection: imagine a hacker could evade §1202 by altering one pixel of a photo and claiming it’s not identical. The issue has come up recently in cases involving AI-generated outputs: if an AI system trains on copyrighted data and produces pieces of it without attribution, is that an “identical copy” with CMI removed, or something new? Plaintiffs in those cases argue that §1202 should apply even if the output isn’t a verbatim copy, so long as CMI was removed from material that was copied in part. Defendants counter that the law was meant for complete copies and that applying it to partial use would overreach. As of now, federal courts are divided on identicality, and no circuit court has squarely ruled on it.
Practical Enforcement:
Many CMI cases in recent years involve photographers, graphic artists, or musicians whose digital files had metadata or watermarks removed by downstream users. For example, a photographer might license images to a client with attribution required in metadata, but an online platform used by the client automatically strips metadata (a common issue with social media or MLS real estate listings). If infringement then occurs (i.e., third party copying the image), the photographer may claim the platform violated §1202(b). These cases often hinge on proving the platform knew that removing metadata would likely lead to unlicensed copying. To enforce effectively, rightsholders should gather evidence such as industry knowledge that metadata is used to find infringements, the remover’s prior warnings or training about preserving CMI, or direct admissions.
Maintaining good CMI practices is not only a legal safeguard but also part of professional content management. Here are some best practices for business owners, content creators, and users of third-party content:
Always include CMI on your own works:
When you create content (articles, images, videos, software, etc.), attach identifying information. This could be a visible copyright notice (© [Year] [Name]) and contact info, or metadata tags (for digital files) with your name, the title, and any licensing terms. Including CMI from the outset strengthens your position if someone later removes it. It also puts users on notice that the work is protected, reducing accidental infringement. For photographs and graphics, consider embedding a watermark or caption with your name or company, something that marks ownership without overly detracting from the image. Even simple steps like naming digital files in an identifiable way help (e.g., “Acme_Corp_Design2025.jpg” instead of “image123.jpg”).
Preserve existing CMI when using others’ content:
If your business uses content created by someone else (e.g., stock photos, licensed text, or open-source code), do not remove or alter the CMI unless you have clear permission. This applies to both visible attributions and hidden metadata. For instance, if you download a stock photo that has the photographer’s name in the metadata, keep that metadata intact when you publish it, or provide the required credit visibly according to the license. Removing watermarks, cutting off credit lines, or deleting metadata fields can land you in legal trouble under §1202. Many content licenses, including open-source software licenses, actually require retaining copyright notices. Comply with those terms – not just to respect the creator, but because it is a legal requirement. If space is an issue (e.g., a short excerpt where a full credit is hard to include), consult the license or rights holder for how to give attribution in an acceptable way rather than omitting it entirely.
Train your team and configure your tools:
A lot of CMI removal can happen unintentionally. For example, some content management systems or image editing software might not preserve metadata by default. Make sure your employees, contractors, and the tools they use are configured to not strip out CMI by default. Many modern platforms have settings to retain EXIF data or to include attribution. If you run a website, check whether it’s stripping metadata from user-uploaded images; if yes, consider the implications and whether exceptions are needed. Educate anyone handling content on the importance of leaving CMI intact. A policy like “Never remove or edit copyright notices or metadata from third-party content without legal approval” can instill caution. This also applies to developers scraping or processing data; ensure they know not to remove copyright info or author credits from datasets or code.
Document permissions if you do remove CMI:
In some cases, you might have legitimate authority to remove or change CMI. For example, a license to use a photo might allow you to white-label it (replace the original credit with your company’s name), or a contract might let you anonymize content for confidentiality. If you do this, keep records of the contract or email from the copyright owner granting permission. If a question arises, you can demonstrate it was done with the authority of the copyright owner or the law, which is a complete defense.
Use technology to your advantage:
If you’re a creator, there are tools to embed CMI robustly, like metadata and/or digital watermarks. Some systems use information security techniques such as hidden identifiers, such as steganographic watermarks to track works. While not foolproof, these can complement legal CMI. Similarly, keep identical copies of your originals with full CMI. If someone distributes a version without CMI, having your original helps prove that the only difference is the missing information. Scan the web periodically for your works.
Enforce your rights consistently:
If you discover that your CMI was removed from a distributed work, consider taking action. This might start with a DMCA takedown notice under 17 U.S.C. § 512 if the content is online, or a cease-and-desist letter citing §1202. Often, pointing out the CMI removal and the DMCA’s penalties can prompt a quick settlement or correction. Because of the availability of statutory damages, you have leverage even if actual damages are small. The offending party faces up to $25,000 per violation, which can add up if multiple works or copies are involved. That said, be judicious: accidental or minimal CMI omissions might be resolved amicably, whereas willful and systematic removal (as part of piracy or plagiarism) merits a stronger response, potentially a lawsuit.
In essence, the best practice is transparency: let the attributions and notices flow with the content. From an ethical and business standpoint, it shows respect for creators, and legally it keeps you on the right side of the DMCA CMI rules. Businesses that proactively respect CMI not only avoid lawsuits but also build trust with content partners and audiences.
Copyright management information isn’t just a concern in the United States, it is part of a broader international framework for copyright in the digital environment. Many other countries have provisions analogous to §1202, largely due to the influence of international treaties and agreements. At the international level, the WIPO Copyright Treaty (WCT) (1996) obligates member countries to provide legal protections for “rights management information.” The U.S. implemented this via the DMCA.
Also, the European Union in its Information Society Directive (Directive 2001/29/EC) requires member states to prohibit the removal or alteration of electronic rights-management information. Article 7 of the EU Directive mandates “adequate legal protection” against the removal or tampering of Rights Management Information, and against distribution of works knowing that RMI has been removed. EU member states have implemented this in their national laws, so across Europe it is generally unlawful to knowingly strip off copyright notices or metadata from a work. The RMI concept is the same as CMI and the aim is to safeguard the identification of works and rightsholders in digital commerce.
Countries like Canada and Australia have also have similar provisions, often introduced in the early 2000s. For instance, Canadian copyright law makes it an offense to remove or alter RMI on a work, parallel to the DMCA’s approach. Generally, these laws around the world reflect a common principle: those who distribute copyrighted works in digital form must not meddle with the informational tags that identify the work’s creators, owners, and usage terms.
However, there can be differences in scope and enforcement. Some jurisdictions might not require the same level of scienter (knowledge of likely infringement) as U.S. law. The EU laws, for example, don’t explicitly include the double scienter language of “will induce, enable, facilitate, or conceal infringement.”
For a business operating internationally, the safe move is to treat CMI/RMI as something you should preserve regardless of jurisdiction. Removing metadata or notices can get you in trouble not just in the U.S. but abroad as well. There are also international initiatives and voluntary industry standards aiming to improve content identification. Participating in or adhering to these standards can help demonstrate good faith and compliance globally.
In summary, be aware that foreign jurisdictions also protect copyright management information in line with the WIPO treaty obligations. The core idea is to not remove or falsify the identifying info on a copyrighted work, and is a common thread worldwide.
Copyright Management Information may appear as small text or hidden data attached to a work, but it carries significant legal weight. The DMCA’s provisions on CMI underscore that tampering with this information is not a trivial matter. The takeaways are clear: always maintain accurate CMI with your works, and respect the CMI on others’ works. Doing so not only helps prevent infringement but also shields you from liability under laws like §1202.
If CMI is removed or altered without permission, U.S. law provides robust remedies, from injunctions and damages to potential criminal penalties for willful commercial violations. In practical terms, treating CMI properly is part of good copyright hygiene in the digital content world. It fosters a culture of attribution and accountability. A person acting pursuant to the law will avoid liability and contribute to an ethical creative culture.
If you have an issue relating to copyright management information or copyrights generally, contact our office for a free consultation.
© 2025 Sierra IP Law, PC. The information provided herein does not constitute legal advice, but merely conveys general information that may be beneficial to the public, and should not be viewed as a substitute for legal consultation in a particular case.

"Mark and William are stellar in the capabilities, work ethic, character, knowledge, responsiveness, and quality of work. Hubby and I are incredibly grateful for them as they've done a phenomenal job working tirelessly over a time span of at least five years on a series of patents for hubby. Grateful that Fresno has such amazing patent attorneys! They're second to none and they never disappoint. Thank you, Mark, William, and your entire team!!"
Linda Guzman
Sierra IP Law, PC - Patents, Trademarks & Copyrights
FRESNO
7030 N. Fruit Ave.
Suite 110
Fresno, CA 93711
(559) 436-3800 | phone
BAKERSFIELD
1925 G. Street
Bakersfield, CA 93301
(661) 200-7724 | phone
SAN LUIS OBISPO
956 Walnut Street, 2nd Floor
San Luis Obispo, CA 93401
(805) 275-0943 | phone
SACRAMENTO
180 Promenade Circle, Suite 300
Sacramento, CA 95834
(916) 209-8525 | phone
MODESTO
1300 10th St., Suite F.
Modesto, CA 95345
(209) 286-0069 | phone
SANTA BARBARA
414 Olive Street
Santa Barbara, CA 93101
(805) 275-0943 | phone
SAN MATEO
1650 Borel Place, Suite 216
San Mateo, CA, CA 94402
(650) 398-1644. | phone
STOCKTON
110 N. San Joaquin St., 2nd Floor
Stockton, CA 95202
(209) 286-0069 | phone
PORTLAND
425 NW 10th Ave., Suite 200
Portland, OR 97209
(503) 343-9983 | phone
TACOMA
1201 Pacific Avenue, Suite 600
Tacoma, WA 98402
(253) 345-1545 | phone
KENNEWICK
1030 N Center Pkwy Suite N196
Kennewick, WA 99336
(509) 255-3442 | phone
2023 Sierra IP Law, PC - Patents, Trademarks & Copyrights - All Rights Reserved - Sitemap Privacy Lawyer Fresno, CA - Trademark Lawyer Modesto CA - Patent Lawyer Bakersfield, CA - Trademark Lawyer Bakersfield, CA - Patent Lawyer San Luis Obispo, CA - Trademark Lawyer San Luis Obispo, CA - Trademark Infringement Lawyer Tacoma WA - Internet Lawyer Bakersfield, CA - Trademark Lawyer Sacramento, CA - Patent Lawyer Sacramento, CA - Trademark Infringement Lawyer Sacrament CA - Patent Lawyer Tacoma WA - Intellectual Property Lawyer Tacoma WA - Trademark lawyer Tacoma WA - Portland Patent Attorney - Santa Barbara Patent Attorney - Santa Barbara Trademark Attorney